Blog contributed by Carlos Kizzee, Executive Vice President of Intelligence Operations & Legal Affairs, RH-ISAC.
As we approach the holiday season, chances are you’re doing more and more online shopping. eCommerce was a big part of most of our lives already, and the pandemic has only reinforced that. But things aren’t always as they seem in the online retail world—sometimes we think we’re buying from one store only to realize we’ve been hijacked and brought somewhere else!
RH-ISAC and The Media Trust are exploring some of the unexpected aspects of online retail in our series, “Crazy Things that Happen in your Online Store Every Day.” In the fourth piece in the series, “Crazy Things You Wouldn’t See in Curbside Pickup,” focuses on customer hijacking. Customer hijacking is an incredibly common occurrence: malicious code or ads running on your store’s page might be stealing your customers and bringing them elsewhere to complete their purchases!
Imagine you’re waiting in line at your favorite grocery store. Your cart is full of the food and produce you need, and you’re getting ready to pay for it all. But you blink, and suddenly you’ve been whisked away to a completely different store, with a cashier you’ve never seen before smiling at you, asking if you’re ready to check out.
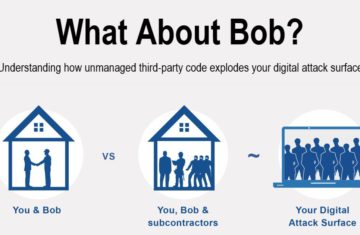
Sounds absolutely crazy, right? But it happens constantly in online stores. Customer hijacking affects all online commerce. Usually some malware or unauthorized code—possible even from ads one the store page—redirects the customer to a completely different site before they’re able to complete their purchase. Obviously if this happens once, it deprives you of a sale. But worse, if it happens often, it can take loyal, repeat customers away from your store, and ultimately devastate your business!
Luckily, there are ways to fix this.
- Monitor all data collection on your site, especially on your cart and checkout pages. Pay special attention to third-party activity. Along with that, monitor all data exfiltration from your site—what’s been collected, and where is it going? How are your cookies set up?
- Have agreements in place with advertising partners, vendors, and third parties around collection of user data on your site. Having clear policies around these issues, following industry best practices, is a huge boon here.
- Scan your sites frequently and from a variety of profiles (as different genders, different platforms and OSes, different geographic locations, etc.). You want to have as comprehensive a view of your vulnerabilities as possible!
The best way to defend your network is to know your network—so frequent scanning, and establishing and enforcing policies about what can and can’t take place on your network are your best friends here. Follow these best practices, and your customers won’t be led astray nearly as often!
RH-ISAC and The Media Trust are looking into more surprising, unexpected, and flat-out crazy things that happen in digital stores that wouldn’t happen anywhere else. Check out the other blogs in this series: