Blog contributed by Carlos Kizzee, Executive Vice President of Intelligence Operations & Legal Affairs, RH-ISAC.
If online shopping wasn’t already part of your daily routine before the pandemic, chances are it is now. As a society, we’re buying far more online than ever before, and that trend is unlikely to slow down. Frustratingly, all that activity brings unwanted attention from the wrong people, and our transactions aren’t always as safe as we assume—even within our own eCommerce sites.
RH-ISAC and The Media Trust are exploring some of the unexpected aspects of online retail in our series, 7 Crazy Things that Happen in your Online Store Every Day. The second piece in this series, “Crazy Things You Wouldn’t See in a Restaurant,” focuses on payment fraud in the customer payment process. As part of this, we conducted a review of restaurant websites and mobile apps, and found quite a bit of unexpected activity present on cart and checkout pages. Unknown and unmonitored activity on payment pages can lead to a host of issues—none of them good for the merchant or the customer.
Skimming is a common eCommerce attack that, as the name implies, “skims” customer information from the cart or the checkout page. In most cases the compromised sale still goes through—so as far as both the retailer and the customer are concerned, everything went fine. But in addition to the merchant getting the customer’s personal and payment information, a malicious actor gets their hands on it as well. Magecart is a well-known skimming attack. And skimming is just one of the ways personal data leakage could occur. Other forms of undetected malicious code, unsecured cookies, or unencrypted transmission methods could all lead to customers’ personal data getting out.
The solution? Continuous client-side scanning and discovery, and a digital risk management plan are the easiest way to avoid this kind of insanity.
- As you scan, please remember to emulate the customer experience, and make purchases as consumers would, through your website, through your mobile app, from different locations. This must be done from outside your network to gain an accurate idea of what goes on when your customers make a purchase. Skimming scams have evolved over time, and simpler detection methods are no longer effective.
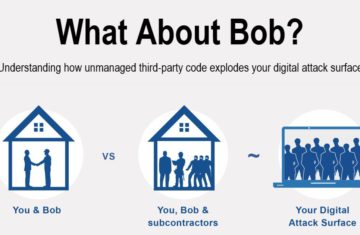
- Review the domains and data collection activity in the purchase journey, particularly in cart, checkout and confirmation pages. High risk items you should shut down include: non-payment processor domains on your payment page, and unauthorized data collection or social media domains on your payment pages. Ensure your digital program adopts a framework and continuous review (weekly, monthly) of the Cart/Checkout process for any changes or anomalies. While your cart and checkout pages are particularly important, knowing which third party services have access to all of your pages is a key step to understanding and mitigating your overall risk.
Just as with the last “Crazy Things” story: best practices are a retailer’s best friend. The more familiar you are with your website, the better you’ll be, so set up policies to restrict what third party applications can reside on your website, and scan it regularly to verify there aren’t any unexpected visitors.
RH-ISAC and The Media Trust are looking into more surprising, unexpected, and flat-out crazy things that happen in digital stores that wouldn’t happen anywhere else. Check out the other blogs in this series: