The Hanna Andersson-Salesforce CCPA settlement highlights the growing fallout for payment-page data breaches
The first CCPA-related legal settlement has landed and, interesting enough, it’s not a regulatory action from the state of California—it’s a CCPA-powered class action suit.
Children’s clothing retailer Hanna Andersson and Salesforce received approval for a preliminary settlement agreement over a data breach occurring between September and November 2019. In addition to a $400,000 settlement fund for victims that had their data stolen, the settlement also requires Hanna Andersson to install a director of cybersecurity and multi-factor authentication for cloud services accounts, as well as conduct a risk assessment consistent with NIST Risk Management Framework.
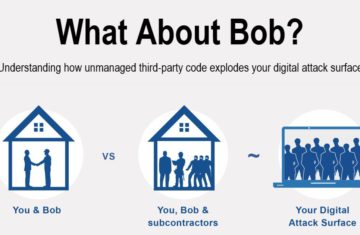
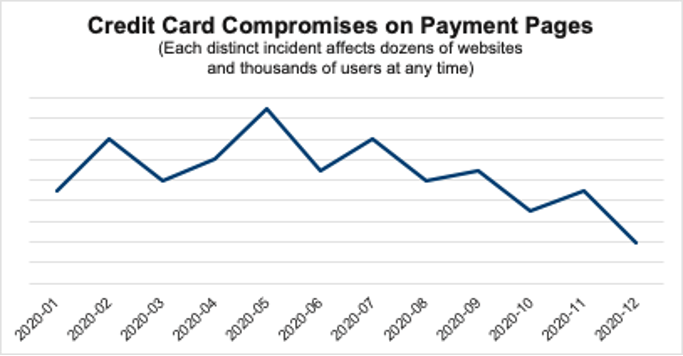
The data breach stems from a Magecart attack, a continued threat affecting any website that accepts credit cards. Magecart is a catchall phrase for a variety of credit-card-skimming scams, and The Media Trust detected a 350% increase in Magecart-related malicious activity over the last year. In particular, there was a big spike in May that correlates with the launch of several small advertising campaigns directed to e-commerce pages with limited security precautions.
Retailers are in jeopardy with CCPA
Magecart is a serious threat for any website taking direct payments from consumers. And as more digital sites enter into the world of e-commerce, fertile hunting grounds are created for malevolent actors. Early stage e-commerce sites become laboratories for bad actors to experiment and perfect their encroachment strategies.
These guys are constantly evolving tactics and they’re deviously patient—as we’ve noted before, scammers enacting Magecart plays are strategic and patient, taking their time with testing and even lying dormant after hacks to avoid detection.
The Hanna Andersson settlement shows that the stakes for security around any commerce program just got higher. A breach is bad news to begin with—the plaintiff in Hanna Andersson claimed customers “face a lifetime risk of identity theft.” It’s difficult to win back shoppers (or grab new ones) after that statement.
But now you can also be held culpable under CCPA—and your service providers can get roped into settlements (and likely fines). A $400,000 settlement fund could be just the tip of the iceberg—take a look at the multi-million dollar fine doled out to British Airways under for data breaches under GDPR. The environment is only going to get stricter when the California Privacy Rights Act (CPRA)—CCPA’s stricter cousin—goes into force in July 2023.
Take the first steps to controlling your website environment
Security is key, and there are steps you can take immediately.
- Apply controlled scanning for malicious code on all the customer journey pages: offer, checkout, payment, and confirmation pages. You should be examining what cookies are dropping on each page, data—for example, what cookies are popping up on the payment pages? What is this vendor doing here? Does it add value for you or your users? Often vendors are left over from past initiatives from different departments and have no value.
- Speaking of vendors, it’s essential to ensure that all third-party code running on your site is coming from authorized vendors on your inclusion list. Catch potential encroachers NOW!
- Scanning doesn’t have to be limited to the customer journey pages. You should be combing your entire site for anomalies and potential emerging threats.
- If you have ads running anywhere on your site, which more and more retailers are experimenting with, you need a creative blocker swiping away all known malware. Malvertising is Magecart’s playground.