Malware on an unsettling trajectory
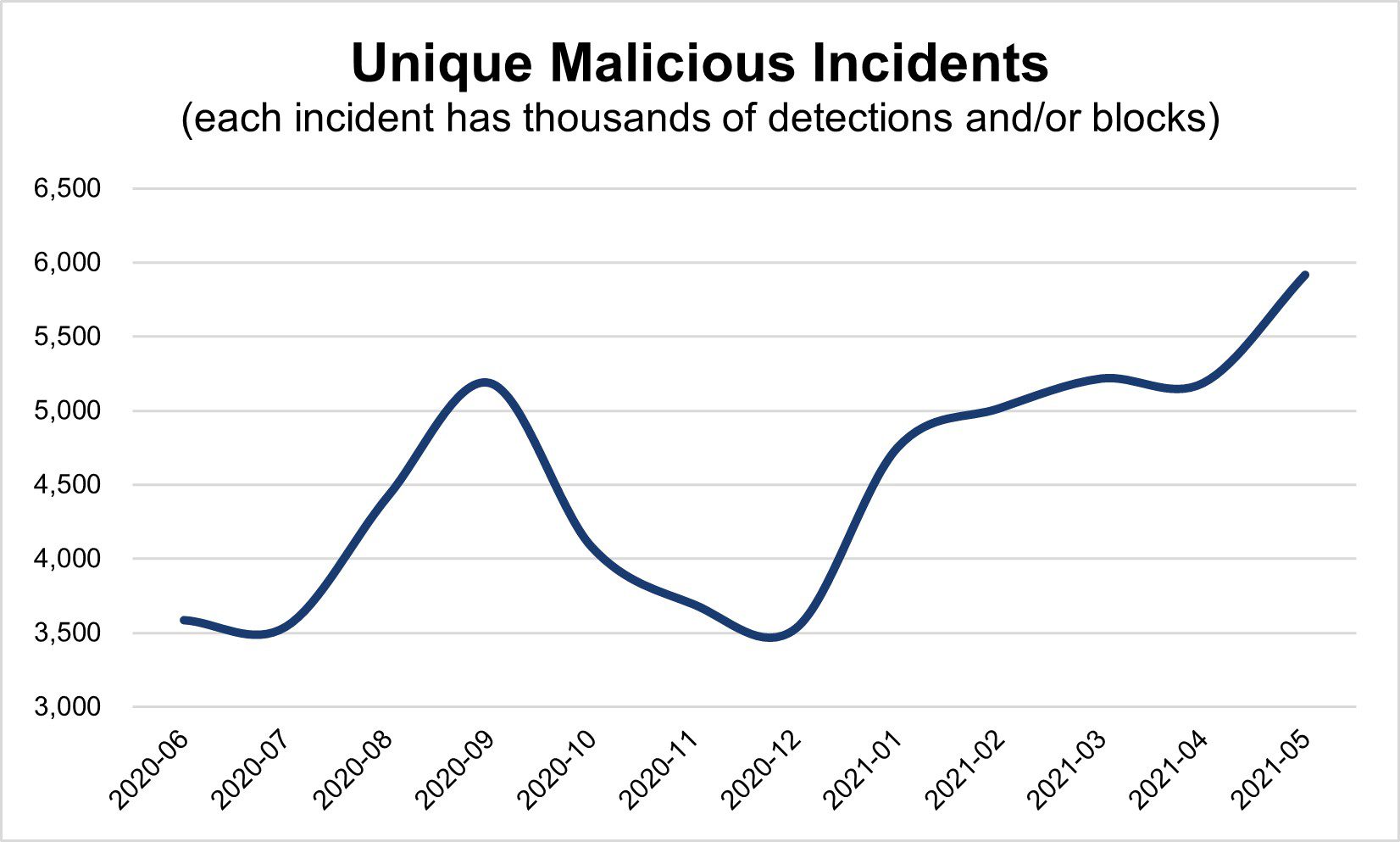
Distinct incidents continue to climb, steadily growing 25% since January. Considering each incident is detected thousands of times during its lifetime, this increase reflects the current state of today’s digital ecosystem.
Key malware behaviors driving incident trajectory:
- Redirects: 78% growth. Content is consistently redirecting to malicious content or auto-redirecting users to an app store without any user initiation.
- Scams: 45% growth. Content entices users to enter personal information for retargeting and reselling purposes, and/or is frequently related to the selling of products delivering false claims.
- Compromised content: 31% growth. A delivered creative or landing page has been altered to be directly involved in the execution of malicious activity—e.g., popups, fake software updates, and exploit kits.
Malware increased steadily throughout May, keeping our Digital Security & Operations team busy identifying, evaluating, and then addressing outbreaks. Confirmed malicious activity was added to our blocklist and also shared with the offending provider to clean up incidents and keep revenue channels open. (Figure 1)
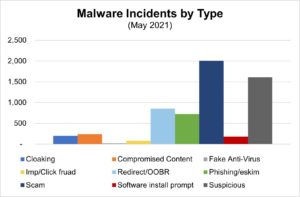
- 2,070 active malicious incidents, on average, managed each day in May
- 34% Scams: Content entices users to enter personal information for retargeting and reselling purposes, and/or is frequently related to the selling of products delivering false claims.
- 27% Suspicious: The campaign exhibits anomalous activity; however, malicious intent is not confirmed. Typically, the domain or content is parked, does not exist, or matches previous patterns or characteristics of known malicious activity.
Interesting Incident: Redirect Barrage
Large-scale redirect campaign started on May 17 and continued through May 22 by cycling through dozens of domains to serve users a fake rewards scheme. What’s interesting is the misplaced recommendation to block the penultimate SSP instead of the malicious campaigns stemming from the malicious buyer on the DSP. This blunt blocking approach causes publishers to lose revenue opportunities. Read more here.