
Explosion in phishing events in May and June 2021 highlights the necessity of click-through scanning
- 4X growth in ad-based phishing since the beginning of 2021, with severe uptick in May and June
- Decline in distinct outbreaks alongside increase in overall hits suggests larger, more enduring campaigns
Recommendations:
- Exhaustive click-through scanning to identify malicious landing pages
- Range of global profiles in client-side scanning for your needs, e.g., targeted geography and surrounding areas
Phishing is often viewed as the province of email scams—for example, the classic message from a suspicious address entices you to sign into your account by clicking a funky link. But phishing lures are also widely deployed on the web via malvertising, and the technique’s popularity is surging as the summer heats up.
The Media Trust detected a 4X growth in phishing events since the beginning of the year—and specifically a massive spike in May 2021 that continued to build through June. [Figure 1] While the majority of episodes were identified in the US, the Digital Security & Operations team has cataloged high numbers of ad-based phishing hits worldwide.
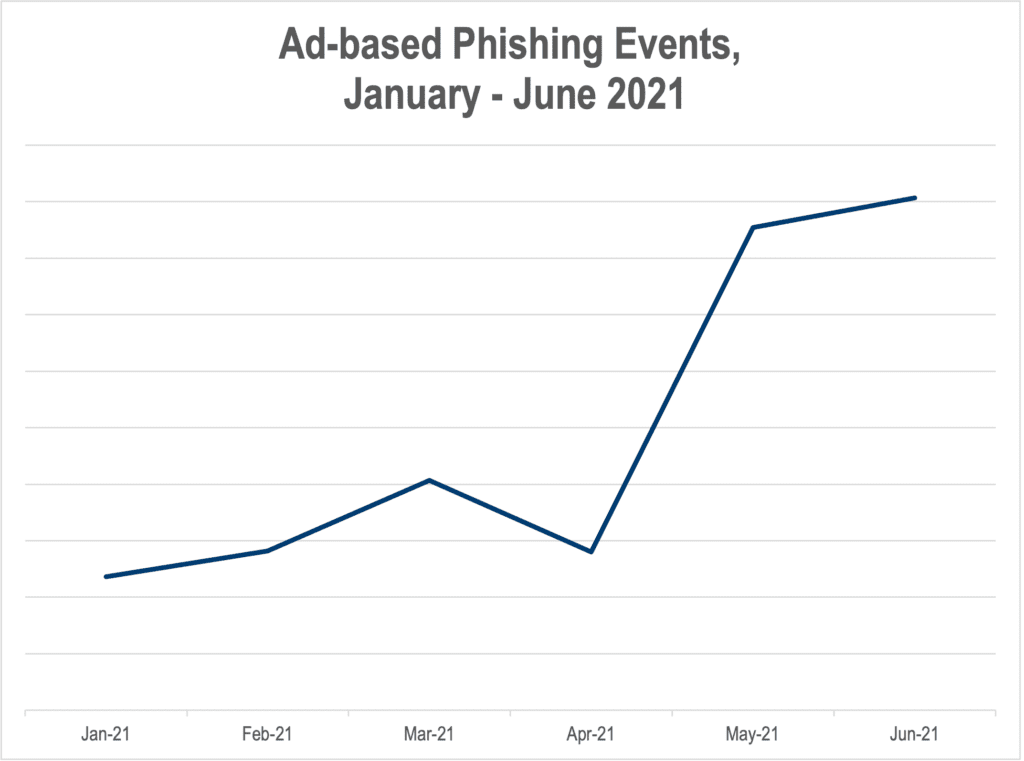
Figure 1: Trajectory for ad-based phishing activity in 2021
The number of distinct outbreaks—typically containing thousands of hits—actually declined slightly in June while overall phishing events are ramping up. This suggests longer, more expansive campaigns that aren’t being shut down quickly. Prominent malvertisers are also showing renewed interest in these kinds of attacks: phishing events powered by mobile-focused Ghostcat-3pc malware spiked in May, more than doubling the month prior.
Catching the Landing Page Hook
Just like its email-based cousin, web phishing attempts to pilfer a variety of personal data points from users, from emails and phone numbers all the way to US Social Security Numbers and other highly sensitive information. Creatives often revolve around bogus sweepstakes, fake contests, and nonexistent rewards. [Figure 2]
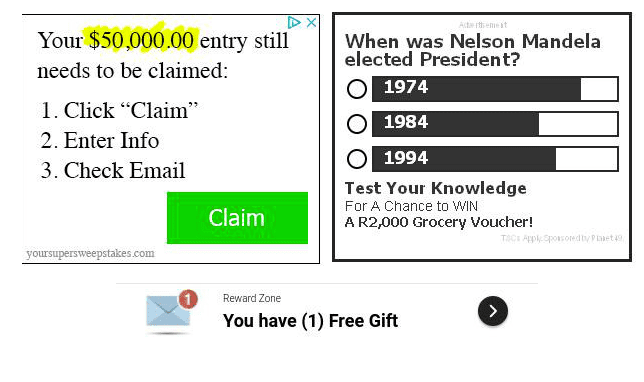
Figure 2: Sample creative used in ad-based phishing incidents
Phishing attacks can be difficult to identify without click-through scanning to analyze malicious landing pages. While the creative may contain the bait to grab a consumer click, it’s the landing page that provides the hook—and gives away the venomous nature of the campaign. [Figure 3]
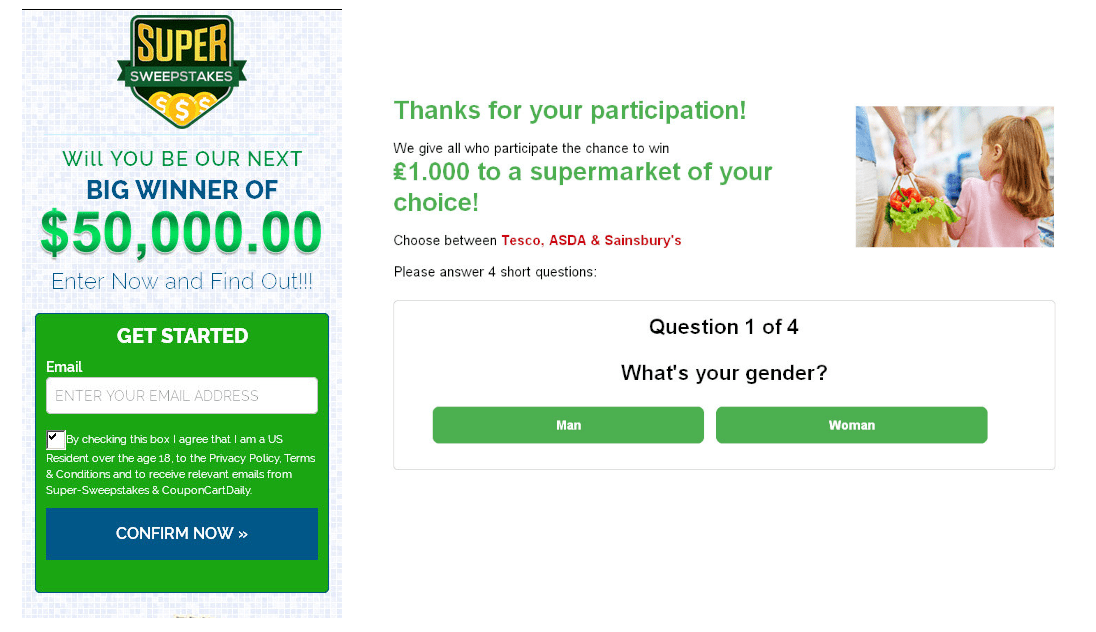
Figure 3: Figure 3: Phishing landing pages luring personal information out of unsuspecting consumers via bogus offers.
Phishing License Revoked
Alongside the rise of malicious clickbait, this surge in ad-based phishing points to malvertisers diversifying strategies beyond the redirect. AdTech companies and publishers merely focusing on that attack vector are leaving consumers exposed to other highly pernicious scams. Swindled personal data could later be sold on the dark web and used to propagate ransomware campaigns.
Click-through scanning is key to identifying and then shutting down these phishing campaigns, rather than letting them endure and stalk more potential victims.



